Hi,
We were able to further localize this problem and found the problem is with the function "BIO_dgram_sctp_wait_for_dry". In this function after enabling the "sctp_sender_dry_event" we are trying to do MSG_PEEK to peek to the message at SCTP layer, in this case the size of the message waiting in the lower layer is 15 which size is exactly the size of "Handshake Alert" that is received from the server and waiting to be read. Dry event is never read from the lower layer that causes the SUB_STATE_ERROR and intern causes the SSL_Connect to loop in application.
Current version of openssl we are using is 01.01.00g.
We have tested and able to reproduce this issue with the OPENSSL 01.00.02k version that is packaged with RHEL 7.4 as well.
Thanks,
Mahesh G S
On Mon, Nov 20, 2017 at 4:42 PM, mahesh gs <mahesh116@xxxxxxxxx> wrote:
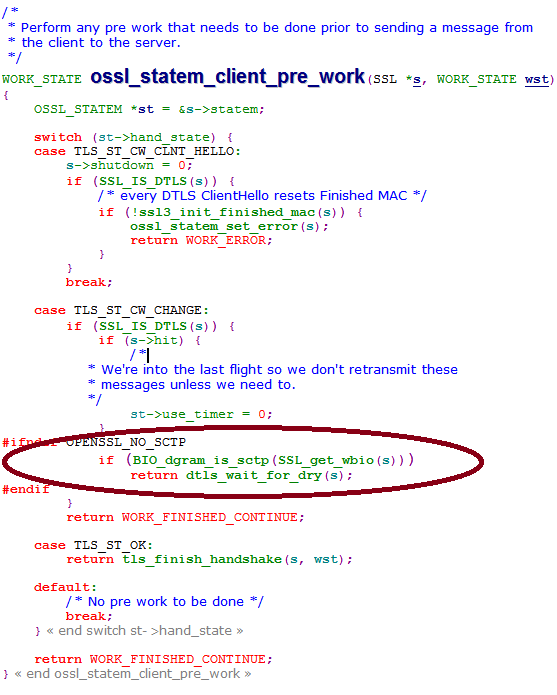
Hi Matt,Thanks for the response.We debugged through openssl code to get to know the reason why client is not reading "SSL Alert".Once the "ClientKeyExchange" is sent openssl trying to send out the "ChangeCipherSpec" message which is creating the problem.The pre-work function for "ChangeCipherSpec" enables SCTP dry event and wait for dry event notification.In this scenario, dry notification is never sent from SCTP. "dtls_wait_for_dry" always returns "WORK_MORE_A". Hereafter flow never enters "read_state_machine" where alert is to be red.This causes SSL_Connect to be in infinite loop.Thanks,Mahesh G SOn Fri, Nov 17, 2017 at 3:36 PM, Matt Caswell <matt@xxxxxxxxxxx> wrote:
On 17/11/17 06:42, mahesh gs wrote:
> Why
> does client respond with "Client key exchange" even if the the handshake
> failure alert is sent from server?
The client will send its entire flight of messages before it attempts to
read anything from the server. So, in this case, the ClientKeyExchange
message is still sent because the client hasn't read the alert yet.
Matt
--
openssl-users mailing list
To unsubscribe: https://mta.openssl.org/mailman/listinfo/openssl-users
-- openssl-users mailing list To unsubscribe: https://mta.openssl.org/mailman/listinfo/openssl-users